How To Create Running Check Register In Excel
If y'all've e'er wondered how software pirates can have software and crack it time and time again, fifty-fifty with security in place, this minor series is for you. Fifty-fifty with today'south most advanced methods of defeating piracy in place, it is still relatively easy to fissure almost any program in the world. This is mainly due to computer processes' ability to be completely manipulated by an assembly debugger. Using this, yous can completely featherbed the registration procedure by making it skip the application's key code verification procedure without using a valid key. This works because assembly allows you to speak directly to the processor and force a skip over the registration process.
In this Aught Byte, let's go over how corking could work in practice by looking at an example program (a program that serves no purpose other than for me to hack). I will not exist walking you lot through how to actually crack a legitimate program, because I can't just scissure a program for demonstration, but the techniques applied to my examples should give you lot the foundation needed to create your ain. At that point, it'south a exam of your morals if you desire to use your cognition for good or bad.
Requirements
- Windows (for examples only, debuggers exist beyond platforms)
- A debugger installed: IDA, ollydbg, etc. (ollydbg will be used in examples)
Step 1 Test the Program
Beginning, run the plan that you are attempting to reverse engineer and attempt to activate it with a random fundamental to verify that yous demand a valid software cardinal to proceed. This is to verify that we tin come up with the keys.
Step 2 Run the Program in a Debugger
- Run ollydbg.
- Open up up the plan you wish to bypass with ollydbg.
- Click the play button to run the program with the debugger attached.
- Right click the CPU window, and click Search For > All intermodular calls.
- Search for high interest DLLs. GETDLGITEMTEXT, volition exist for dialog boxes, which get called when y'all try to enter a software fundamental. By stepping into the role with the debugger, we tin examine the registration specifically. SENDDLGITEM could be used besides.
- Test to meet which ane works to suspension out of the activation loop by right clicking the DLL phone call and setting a breakpoint for all instances of that call.
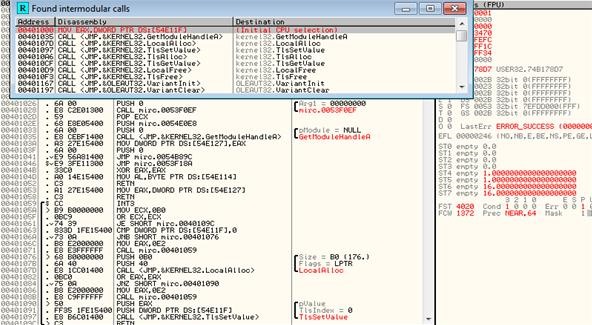
- Resume the program and enter whatsoever software key you lot feel similar. If the debugger breaks (pauses the program'south execution) after entering your key, and then you know you found DLL in step v.
- Press F8 back in the CPU window to force the next footstep until you get to the TEST EAX. EAX is the return of a value, which means that a bank check is being performed hither. Upon examination, we can meet that the EAX is checking for a number that is not equal to a null value. This means that if information technology is replaced with anything other than nix, it will run.

- Right-click the EAX and change it in hex value to 1, instead of 0.
- Resume the program again, and you will have successfully activated the program.
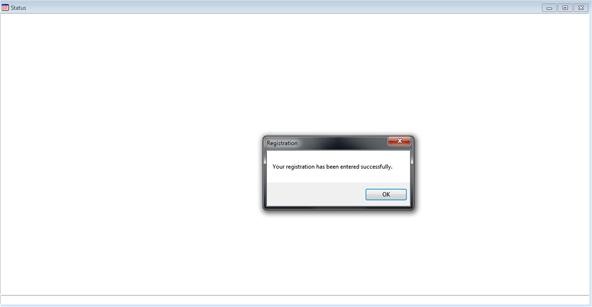 And for proof it was registered to me:
And for proof it was registered to me: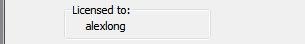
This works considering you are making the process spring from one register and skip the one that verifies the key entered. To exploit the key registration algorithm, keep an eye out for office 2 of this tutorial on making the key generator. Hooray for assembly!
- Post to the forums
- Chat on IRC
- Follow on Twitter
- Circle on Google+
Want to first making money as a white chapeau hacker? Spring-start your hacking career with our 2020 Premium Upstanding Hacking Certification Preparation Bundle from the new Null Byte Shop and get over sixty hours of preparation from cybersecurity professionals.
Purchase At present (ninety% off) >
Other worthwhile deals to cheque out:
- 97% off The Ultimate 2021 White Hat Hacker Certification Package
- 99% off The 2021 All-in-One Data Scientist Mega Bundle
- 98% off The 2021 Premium Acquire To Code Certification Packet
- 62% off MindMaster Listen Mapping Software: Perpetual License
Source: https://null-byte.wonderhowto.com/how-to/hacks-behind-cracking-part-1-bypass-software-registration-0132568/
Posted by: randallextelown67.blogspot.com


0 Response to "How To Create Running Check Register In Excel"
Post a Comment